Side Channel Attacks: Not Just Hardware Tricks—They’re Spilling into Cyber Threat Intelligence!
When we hear “side-channel attacks,” many of us think of obscure hardware exploits involving power fluctuations, timing discrepancies, or EM emissions. Nerdy stuff, right? But what if I told you that side-channel techniques aren’t limited to microchips and circuits? They’re making waves in the world of Cyber Threat Intelligence (CTI).
Let’s dig into a fascinating example: Russia’s geofencing practices during geopolitical conflicts. Sounds like the plot of a cyber-espionage thriller? Well, it kind of is.

Russia’s Geofencing: The Digital Iron Curtain
Here’s what was happening, as highlighted in a 2022 report on Russian geofencing:
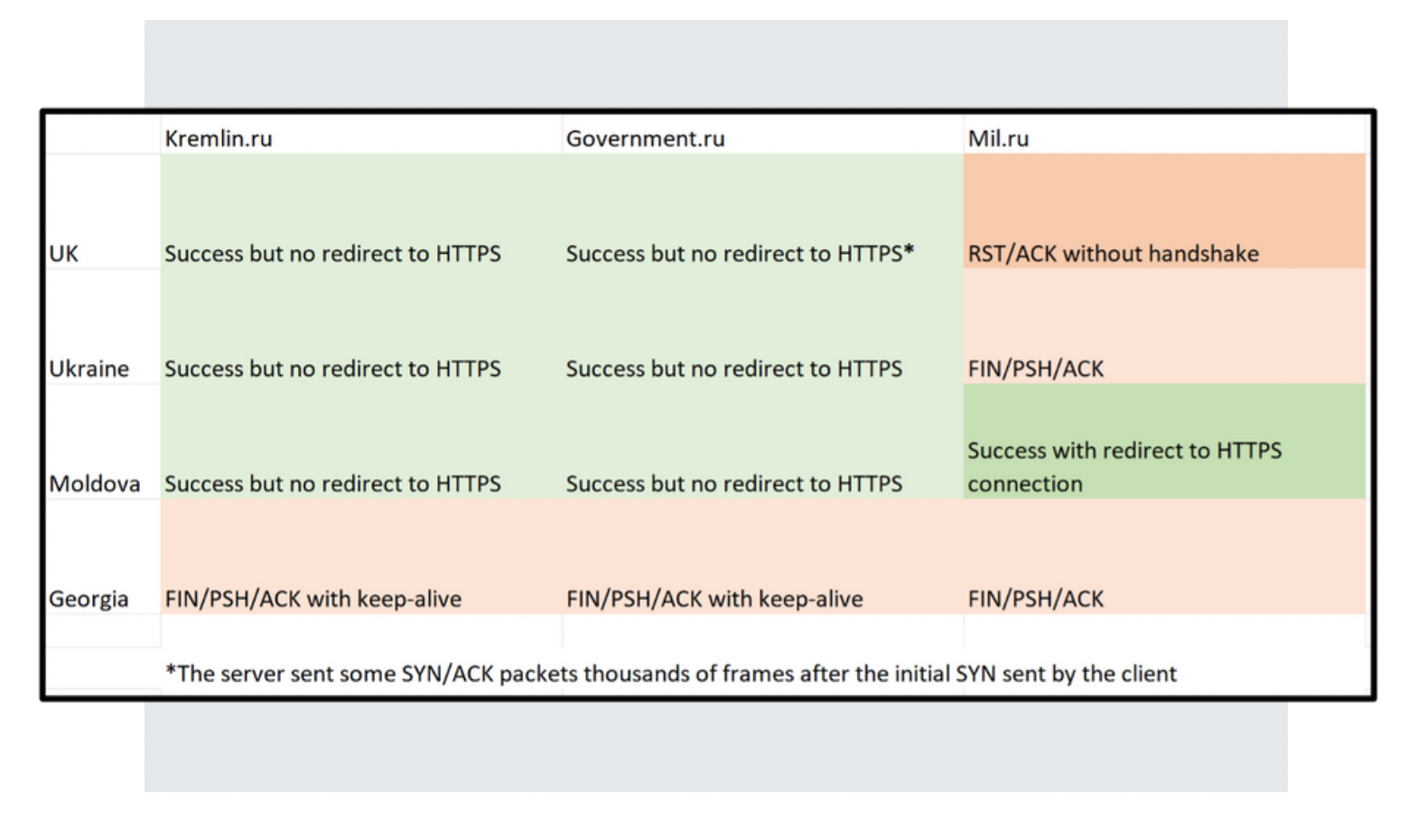
- Georgia: Blocked entirely. It’s like slamming the door and throwing away the key.
- Moldova: Open-door policy—come on in, no restrictions. Weird, right?
- Ukraine: Slow internet with access denied to Russian military domains. Think of it as a bouncer letting you into the party but keeping you out of the VIP section.
- The UK: Mostly unrestricted access, like being a regular guest but still watched closely.
What Does This Have to Do with Side Channels?
Now, here’s where things get juicy. These access restrictions weren’t just about keeping information secure but they were sending side-channel signals to the rest of the world. Let’s break it down:
-
Threat Perception: Blocking Georgia completely screams, “We see you as a major threat.” On the flip side, Moldova’s free pass says, “You’re not on our radar. Chill.”
-
Protecting the Crown Jewels: Ukraine’s restricted access to military domains was Russia’s way of saying, “Hands off our sensitive stuff!”
-
Propaganda Control: By controlling who sees what, Russia could manipulate narratives, steering public opinion at home and abroad. Who needs to hack when you can just curate the truth?
CTI Lessons from Side-Channel Signals
For CTI pros, these side-channel insights are gold. They reveal not just what an adversary is doing but also why. Every geofencing decision tells a story about priorities, vulnerabilities, and strategic thinking.
Think of it like overhearing someone’s tone of voice in an argument. They don’t outright say what’s bothering them, but the side-channel (the tone) gives it away. In this case, geofencing is the tone, and Russia’s actions are the words. Clever, right?
Why It Matters
Understanding side-channel techniques in CTI is like having a decoder ring for your adversary’s intentions. It’s no longer just about finding the bad guy with malware or patching up your defenses. It’s about outthinking them, using their own actions as breadcrumbs to predict their next move.
So next time you hear “side-channel attacks,” don’t just think hardware. Think geopolitics, think digital espionage, think geofencing and realize the game is much bigger than you thought.
Cybersecurity is evolving, and if you’re paying attention, the side-channels are shouting secrets louder than ever. You just have to know how to listen.
Resources
- Darkbeam - Geofencing by Russia: https://hubs.ly/Q0164Q0c0